#blockchain-security
#blockchain-security
[ follow ]
#quantum-computing #cryptography #post-quantum-cryptography #bitcoin #defi #ethereum #smart-contracts
fromCointelegraph
6 months agoApplied MEV protection via Shutter's threshold encryption
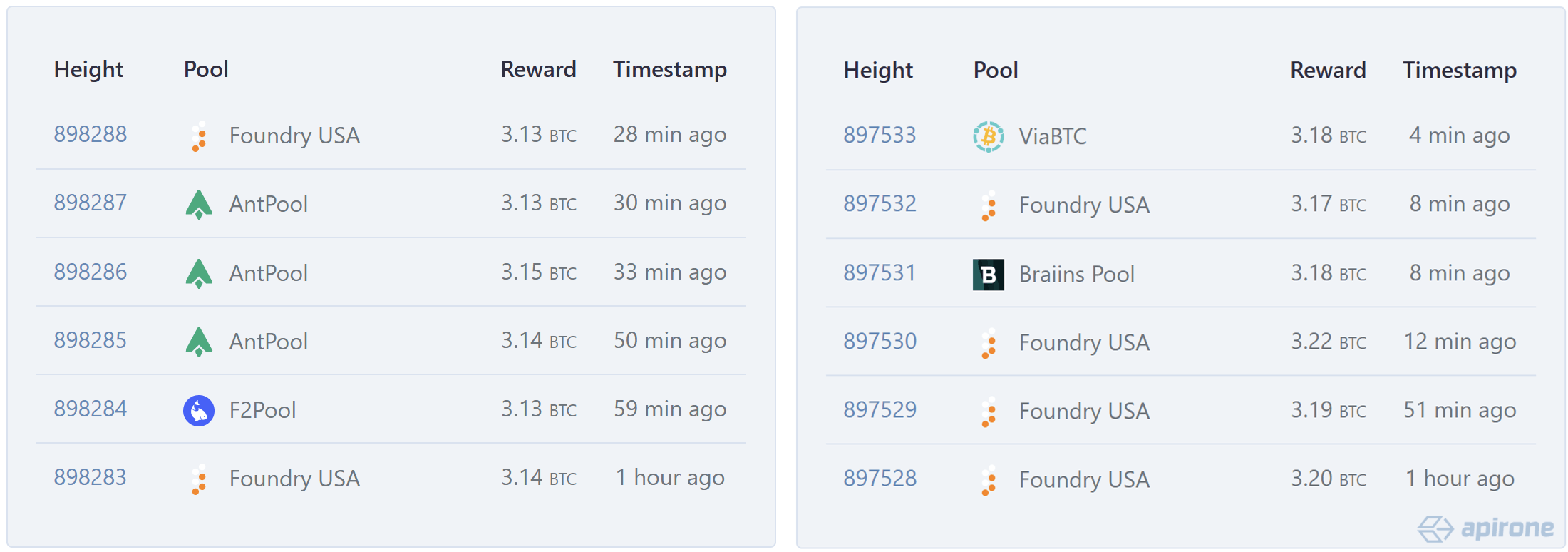
MEV is especially notorious on Ethereum, where it continues to be extracted at a rate equivalent to 11% of block rewards. Data shows that nearly $300,000 was lost in sandwich attacks in September. This reveals that MEV is a recurring hidden fee, not a minor inefficiency, hitting large trades hardest in volatile markets.
Cryptocurrency
fromCointelegraph
5 months agoHow Batched Threshold Encryption could end extractive MEV and make DeFi fair again
On most modern blockchains, transaction data is publicly viewable in the mempool before it is sequenced, executed and confirmed in a block. This transparency creates avenues for sophisticated parties to engage in extractive practices known as Maximal Extractable Value (MEV). MEV exploits the block proposer's ability to reorder, include or omit transactions for financial gain.
Cryptocurrency
fromThe Hacker News
2 months agoKonni Hackers Deploy AI-Generated PowerShell Backdoor Against Blockchain Developers
The North Korean threat actor known as Konni has been observed using PowerShell malware generated using artificial intelligence (AI) tools to target developers and engineering teams in the blockchain sector. The phishing campaign has targeted Japan, Australia, and India, highlighting the adversary's expansion of the targeting scope beyond South Korea, Russia, Ukraine, and European nations, Check Point Research said in a technical report published last week.
Information security
Information security
fromArs Technica
3 months agoSupply chains, AI, and the cloud: The biggest failures (and one success) of 2025
Supply-chain attacks surged in 2024–2025, allowing attackers to compromise single targets and infect thousands or millions of downstream users, causing widespread theft and outages.
fromTheregister
5 months agoAttackers dig up $11M in Garden Finance crypto exploit
In a statement issued on Friday, Garden again said that user funds were safe and that the attack exploited one of its solvers. In the context of decentralized finance, a solver is typically an algorithm or trading agent that's relied on to execute transactions in the most efficient manner possible. Garden is a blockchain bridge protocol company, and its solvers earn a small profit for carrying out transactions between blockchains.
Information security
[ Load more ]