#chinese-state-sponsored-hacking
#chinese-state-sponsored-hacking
[ follow ]
#cybersecurity #malware #iran #vulnerabilities #china #north-korea #spyware #axios #espionage #hacking #fbi
fromFast Company
2 days agoChina is moving faster on next-gen tech. The U.S. is trying to keep up
In recent weeks, China approved the world's first commercial brain-computer interface medical device and unveiled a five-ton class electric vertical takeoff and landing aircraft that has already completed a public flight.
Science
Intellectual property law
fromIPWatchdog.com | Patents & Intellectual Property Law
14 hours agoOther Barks & Bites for Friday, April 3: Trump EO Sets 100% Tariffs on Patent Pharmaceutical Imports; Squires Vacates TikTok IPRs Under Tianma Microelectronics; and Kallay Voices DOJ's Preference for FRAND Obligations
President Trump signed an executive order imposing 100% tariffs on imported patented pharmaceuticals and ingredients from 17 drugmakers.
fromComputerworld
12 hours agoA core infrastructure engineer pleads guilty to federal charges in insider attack
Rhyne's attack involved unauthorized remote desktop sessions, deletion of network administrator accounts, and changing of passwords, showcasing significant security vulnerabilities.
Information security
Intellectual property law
fromFuturism
18 hours agoAnthropic Suddenly Cares Intensely About Intellectual Property After Realizing With Horror That It Accidentally Leaked Claude's Source Code
Anthropic's copyright takedown request for its AI model's source code highlights hypocrisy in its stance on copyright laws.
Artificial intelligence
fromComputerWeekly.com
1 month agoUS artificial intelligence developers accuse Chinese firms of stealing their data | Computer Weekly
US AI developers report Chinese competitors using distillation attacks to extract model data, while facing accusations of training models on unlicensed data themselves.
Privacy technologies
fromwww.theguardian.com
1 month agoChinese technology underpins Iran's internet control, report finds
Iran's internet control relies heavily on Chinese surveillance technologies and infrastructure, enabling near-total blackouts and refined censorship that facilitate human rights abuses.
#cyberespionage
Information security
fromSecurityWeek
2 weeks agoChina-Linked Hackers Hit Asian Militaries in Patient Espionage Operation
China-linked cyberespionage campaign CL-STA-1087 has targeted Southeast Asian military organizations since at least 2020, using custom backdoors and credential stealers to extract military intelligence and Western collaboration details.
Information security
fromThe Hacker News
3 weeks agoChinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
A China-based cyber espionage operation has targeted Southeast Asian military organizations since at least 2020, using custom backdoors and credential harvesters for strategic intelligence collection on military capabilities and Western armed forces collaboration.
fromTheregister
3 weeks agoChina's CERT warns OpenClaw can inflict nasty wounds
The CERT warned that OpenClaw has "extremely weak default security configuration" and must therefore be handled with extreme care. The CERT is worried that attackers can target the tool by embedding malicious instructions in web pages, and that poisoned plugins for the agentic tool can put users at risk. China's cyber-advisors also point out that OpenClaw has already disclosed several severe vulnerabilities that can result in credential theft.
Information security
Information security
fromTechzine Global
4 weeks agoChina and spyware companies dominate zero-day attacks
Zero-day vulnerability exploits reached 90 cases in 2025, with Chinese cyber espionage groups and commercial spyware companies driving attacks increasingly toward enterprise infrastructure and security equipment.
Information security
fromTheregister
1 month agoGoogle and friends disrupt suspected Beijing espionage op
Google disrupted UNC2814, a China-linked group conducting widespread cyberattacks on telecommunications and government organizations across multiple continents using Google Sheets API for command-and-control operations.
Information security
fromNextgov.com
1 month agoChinese telecom hackers likely holding stolen data 'in perpetuity' for later attempts, FBI official says
Chinese state-backed Salt Typhoon likely retains stolen telecom data indefinitely for surveillance, future exploitation, and aggregation with other exfiltrated information.
fromSecurityWeek
1 month agoChina Revives Tianfu Cup Hacking Contest Under Increased Secrecy
Tianfu Cup was launched as an alternative to the Zero Day Initiative's Pwn2Own competition, which regularly pays out more than $1 million to white hat hackers who demonstrate critical vulnerabilities in consumer and enterprise hardware and software, industrial control systems, and automotive products. Tianfu Cup made headlines in 2021, when participants earned a total of $1.9 million for exploits targeting Windows, Ubuntu, iOS, Microsoft Exchange, Chrome, Safari, Adobe Reader, Asus routers, and various virtualization products.
Information security
Information security
fromThe Hacker News
1 month agoChina-Linked Amaranth-Dragon Exploits WinRAR Flaw in Espionage Campaigns
China-linked Amaranth-Dragon (APT41-associated) carried out stealthy, narrowly focused cyber espionage against Southeast Asian government and law enforcement, exploiting WinRAR CVE-2025-8088.
fromThe Hacker News
2 months agoChina-Linked UAT-7290 Targets Telecoms with Linux Malware and ORB Nodes
A China-nexus threat actor known as UAT-7290 has been attributed to espionage-focused intrusions against entities in South Asia and Southeastern Europe. The activity cluster, which has been active since at least 2022, primarily focuses on extensive technical reconnaissance of target organizations before initiating attacks, ultimately leading to the deployment of malware families such as RushDrop, DriveSwitch, and SilentRaid, according to a Cisco Talos report published today.
Information security
fromThe Hacker News
2 months agoChina-Linked Hackers Have Used the PeckBirdy JavaScript C2 Framework Since 2023
The cybersecurity company said it identified the PeckBirdy script framework in 2023 after it observed multiple Chinese gambling websites being injected with malicious scripts, which are designed to download and execute the primary payload in order to facilitate the remote delivery and execution of JavaScript. The end goal of this routine is to serve fake software update web pages for Google Chrome so as to trick users into downloading and running bogus update files, thereby infecting the machines with malware in the process.
Information security
fromTheregister
1 month agoGoogle: China's APT31 used Gemini to plan US cyberattacks
A Chinese government hacking group that has been sanctioned for targeting America's critical infrastructure used Google's AI chatbot, Gemini, to auto-analyze vulnerabilities and plan cyberattacks against US organizations, the company says. While there's no indication that any of these attacks were successful, "APT groups like this continue to experiment with adopting AI to support semi-autonomous offensive operations," Google Threat Intelligence Group chief analyst John Hultquist told The Register. "We anticipate that China-based actors in particular will continue to build agentic approaches for cyber offensive scale."
Information security
Information security
fromThe Hacker News
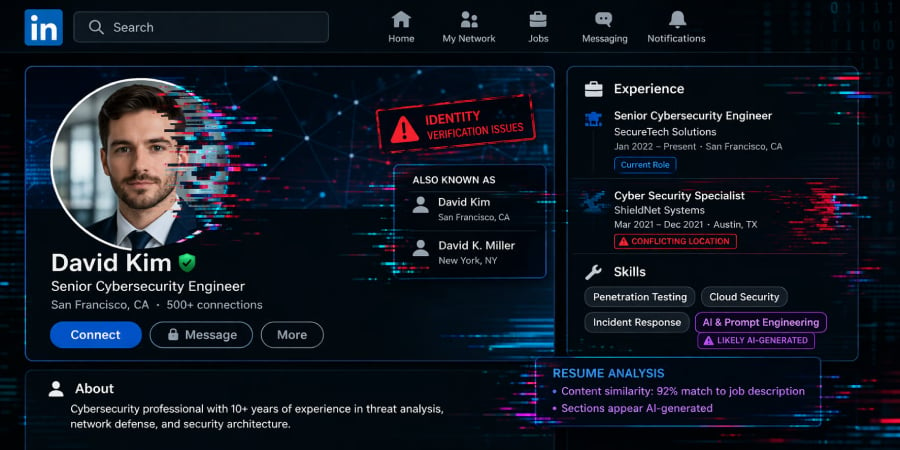
1 month agoGoogle Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
State-sponsored and criminal actors from China, Iran, North Korea, and Russia target the defense industrial base, prioritizing drones, hiring exploitation, edge-device access, and supply-chain risk.
[ Load more ]