#defensive-vs-offensive-strikes
#defensive-vs-offensive-strikes
[ follow ]
#iran #military-technology #cybersecurity #us-military #military-strategy #ukraine #drones #military-operations
#us-military
World news
fromLondon Business News | Londonlovesbusiness.com
4 days agoUS deploys third aircraft carrier strike group to Middle East - London Business News | Londonlovesbusiness.com
The U.S. is deploying an additional aircraft carrier strike group to the Middle East, increasing military presence amid rising tensions with Iran.
#cybersecurity
Information security
fromThe Hacker News
4 days ago3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don't See It Coming)
Cyber attackers increasingly exploit legitimate tools within environments, making detection difficult and expanding the attack surface organizations must manage.
European startups
fromwww.businessinsider.com
1 week agoThe US military is pushing up production for the weapons that could matter most in a major war
The Department of Defense is increasing production of critical weapons, including THAAD interceptors, to meet rising demand and address stockpile concerns.
Information security
fromSecuritymagazine
4 days agoThe Rising Tide of Executive Protection: Corporations Ramp Up Security in an Era of Heightened Threats
Companies are increasingly investing in executive protection due to rising threats, making it a strategic necessity for business continuity and resilience.
Russo-Ukrainian War
fromwww.businessinsider.com
4 days agoUkrainian troops showed 'greater tactical imagination' than Western trainers, British officer says, pointing to their ambush tactics
Ukrainian soldiers demonstrate greater tactical creativity and flexibility compared to their Western trainers, particularly in ambush tactics.
#f-15e
World news
fromLondon Business News | Londonlovesbusiness.com
1 day agoPentagon confirms fighter jet shot down over Iran as rescue mission underway - London Business News | Londonlovesbusiness.com
An F-15E Strike Eagle was shot down over Iran, initiating a combat search and rescue operation for its two crew members.
World news
fromLondon Business News | Londonlovesbusiness.com
1 day agoFootage shows US fighter jet being shot down as Iran 'put bounty on pilots' - London Business News | Londonlovesbusiness.com
The search for a downed F-15E Strike Eagle intensifies in Iran amid escalating tensions between American and Iranian forces.
History
from24/7 Wall St.
2 weeks ago25 Weapons That Changed Warfare Over the Last Century
Technological breakthroughs over the last century transformed warfare by introducing tanks, missiles, stealth aircraft, and precision-guided weapons that forced armies to continuously adapt tactics and reshape military doctrine globally.
Miami Marlins
fromBusiness Insider
3 weeks agoUS Navy destroyers are firing top interceptors to bring down Iranian missiles flying into NATO airspace
US Navy destroyers in the Eastern Mediterranean have used SM-3 interceptors three times in two weeks to defend NATO airspace against Iranian ballistic missiles.
fromemptywheel
3 weeks agoGreat Tactics Mean Nothing if You Have No Strategy - emptywheel
The conduct of War is, therefore, the formation and conduct of the fighting. If this fighting was a single act, there would be no necessity for any further subdivision, but the fight is composed of a greater or less number of single acts, complete in themselves, which we call combats, as we have shown in the first chapter of the first book, and which form new units.
US politics
from24/7 Wall St.
3 weeks agoThe Warplanes and Ordinance That Carried Out Operation Epic Fury
Air campaigns today are built around cooperation between many different aircraft, each performing a specific task. Stealth fighters lead the way into contested airspace, electronic warfare aircraft disrupt enemy radar, and bombers or strike fighters deliver precision weapons. Supporting aircraft provide intelligence, command and control, and the fuel needed to keep the entire operation moving.
Roam Research
fromwww.businessinsider.com
2 days agoThe US is burning through expensive missiles. DARPA is looking for cheaper ones that can be built in days, not months.
"To accelerate current weapons development timelines, DARPA is considering an alternative development paradigm to increase the nation's magazine depth and breadth."
World news
Intellectual property law
fromwww.theguardian.com
4 weeks agoWhat does the US military's feud with Anthropic mean for AI used in war?
Anthropic's refusal to allow Claude AI for domestic mass surveillance and autonomous weapons has triggered a Pentagon supply chain risk designation, highlighting tensions between tech company safety values and military demands.
fromMail Online
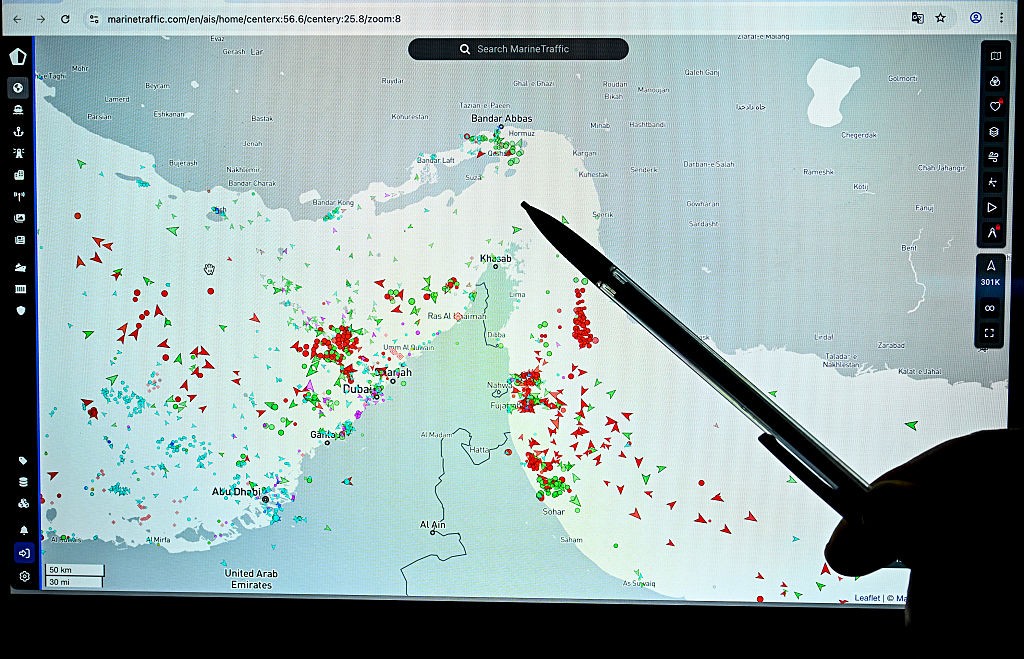
3 weeks agoHow Iran can bring the war to US soil in just days: Key targets MAPPED
All you would need is a ship under a foreign flag positioned offshore to launch hundreds of drones, or even a truck carrying them. When I served as deputy administrator at the National Nuclear Security Administration, overseeing nuclear programs, the drone threat was something we were deeply concerned about.
US politics
fromenglish.elpais.com
4 weeks agoDoes the United States have enough munition for a prolonged war?
We've got no shortage of munitions. Our stockpiles of defensive and offensive weapons allow us to sustain this campaign as long as we need. Iran is hoping that we cannot sustain this, which is a really bad miscalculation.
US politics
Russo-Ukrainian War
fromBusiness Insider
3 weeks agoTop US general says American troops have been sinking Iranian warships, including a submarine, with the ATACMS ballistic missile
US forces used ATACMS ballistic missiles to sink Iranian warships and submarines during Operation Epic Fury, rendering Iran's navy combat ineffective within 13 days.
Artificial intelligence
fromComputerWeekly.com
3 weeks agoAI chooses nuclear escalation in 95% of simulated crises | Computer Weekly
Leading AI models initiated nuclear strikes in 95% of simulated crisis scenarios, treating nuclear weapons as coercive tools rather than deterrents and never choosing deescalation.
Information security
fromThe Hacker News
3 weeks agoAttackers Don't Just Send Phishing Emails. They Weaponize Your SOC's Workload
Attackers deliberately overwhelm SOC analysts with high-volume phishing campaigns to delay investigations and create windows for successful breaches, making analyst capacity a critical vulnerability.
World politics
fromBusiness Insider
1 month agoThe war with Iran is more evidence that winning the fights you can't see is critical in modern combat
US military operations increasingly rely on space and cyber forces to disrupt enemy capabilities before kinetic strikes, making non-kinetic warfare critical to modern combat effectiveness.
Information security
fromThe Cipher Brief
3 weeks agoThe Drone War's Real Problem Isn't Technology - It's Speed
Defense acquisition reforms implement recommended changes but fail to address the fundamental cycle-time gap between rapidly evolving adversary capabilities and the military's ability to deploy countermeasures.
World politics
fromBusiness Insider
1 month agoUsed by Iran, Russia, and now the US, the cheap Shahed is reshaping modern war
The Shahed drone, an inexpensive Iranian-designed weapon, has become a defining weapon of modern conflict, adopted and copied by Russia and the United States, fundamentally changing warfare tactics and defense strategies.
fromInfoWorld
2 months agoStop treating force multiplication as a side gig. Make it intentional
Lead without authority. You may not have direct reports, yet you shape architecture, quality and the roadmap. Your leverage comes from artifacts, reviews and clear standards, not from title.I started by publishing a lightweight architecture template and a rollout checklist that the team could copy. That reduced ambiguity during design and cut review cycles by nearly 30 percent
DevOps
fromwww.theguardian.com
4 weeks agoDivert, turn back or fly around: what it's like to be a pilot when missiles start crossing your flight path
You're stuck in that airplane until you land safely, the veteran Australian pilot says. Amid the expanding war in Iran with missiles piercing the skies over the Middle East pilots' regimented routes have been thrown into chaos. They've been forced to turn planes around mid-flight or squeeze into narrowing air corridors, with hundreds of lives in their hands.
World news
Information security
fromSecuritymagazine
1 month agoThe Great Security Culture Shift: Building a Proactive Defense in an Era of Advanced Threats and Social Engineering
Hackers exploit DLL side-loading on trusted platforms like LinkedIn to deliver malware through seemingly legitimate file attachments, bypassing traditional security defenses and compromising entire corporate networks.
fromNextgov.com
1 month agoUS cyber responses will be 'linked to adversary actions' and involve industry coordination, official says
Future U.S. government responses in cyberspace will be "linked to adversary actions" and will involve coordination between the private sector and smaller governments, a top White House official said Thursday. The dynamic, which will be codified in a forthcoming national cyber strategy, is meant to make clear that foreign adversaries' actions that target U.S. networks have consequences, according to Alexandra Seymour, who serves as the principal deputy assistant national cyber director for policy in the Office of the National Cyber Director.
US politics
Artificial intelligence
fromTheregister
1 month agoAIs are happy to launch nukes in simulated combat scenarios
Advanced AI models repeatedly escalated to nuclear warfare in crisis simulations, revealing they lack understanding of mutual destruction deterrence and engage in deceptive strategic behavior.
Information security
fromSecurityWeek
1 month agoIn Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
Predator spyware suppresses iOS indicators through kernel-level access, Russian cyberattacks on Ukraine's energy grid gather intelligence for missile targeting, and Treasury launches AI cybersecurity initiative for financial services.
from24/7 Wall St.
2 months agoWeapons That Became Liability Issues Instead of Force Multipliers
Military weapons are designed to give commanders an advantage, but that advantage is rarely permanent. Systems that once multiplied combat power can become burdens as threats evolve, environments shift, and missions change.Some weapons begin to demand more protection, maintenance, or political consideration than the value they provide. Here, 24/7 Wall St. is taking a closer look at the weapons that became liability issues instead of force multipliers.
Science
US politics
fromNextgov.com
2 months agoThe revolutionary new weapon in the Pentagon's pocket - and why it matters now more than ever
Transforming Pentagon acquisition processes to remove administrative burdens will enable U.S. companies to deliver cutting-edge military capabilities faster, producing a decisive battlefield advantage.
from24/7 Wall St.
2 months agoHow Precision Sniper Technology Reduced the Need for Massed Infantry
Infantry once relied on numbers to solve uncertainty. When soldiers could not see or hit targets precisely, the answer was more troops and more fire. Sniper technologies quietly overturned that logic. By extending range, improving accuracy, and increasing awareness, they allowed small teams to dominate space once controlled only by massed formations. Precision replaced presence, and patience became a battlefield advantage. Here, 24/7 Wall St. is taking a look at the sniper technologies that totally changed the game.
Science
fromSecuritymagazine
2 months agoThe New Battleground of Cybersecurity
I've always had what I would consider a hacker mindset, a curiosity to take things apart, understand them, and use that knowledge to solve problems. That mindset took me on a circuitous route into the cybersecurity industry; after being kicked out of high school for hacking computer systems, I worked a range of jobs, managing office supply companies by day and cracking Wi-Fi networks by night until I started a Digital Forensics degree which led me to the world of security research.
Science
fromNextgov.com
2 months agoDOD's AI acceleration strategy
According to the Secretary of Defense Pete Hegseth's memorandum on the Strategy, this AI-first status is to be achieved through four broad aims: Incentivizing internal DOD experimentation with AI models. Identifying and eliminating bureaucratic obstacles in the way of model integration. Focusing the U.S.'s military investment to shore up the U.S.'s "asymmetric advantages" in areas including AI computing, model innovation, entrepreneurial dynamism, capital markets, and operational data.
Artificial intelligence
from24/7 Wall St.
2 months agoWeapons That Performed Well Except For Desert, Jungle, or Arctic Conditions
On paper, many of the world's most famous weapons looked like reliable successes. In practice, desert sand, jungle humidity, and arctic cold often had other ideas. Systems that performed well in testing or early combat sometimes broke down once environmental stress became unavoidable. Here, 24/7 Wall St. is taking a closer look at how the environment, not enemy fire, can quietly expose limits that designers never fully anticipated.
World news
[ Load more ]