Privacy technologies
fromTNW | Insights
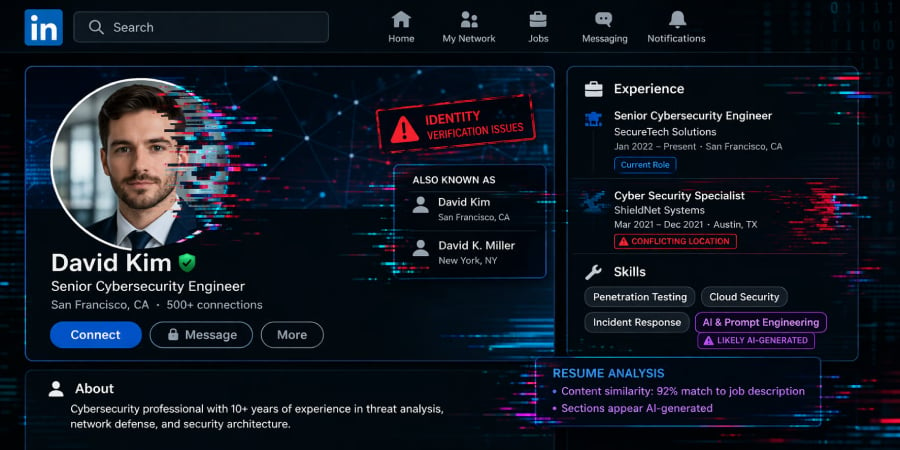
17 hours agoLinkedIn secretly scans 6,000+ browser extensions and fingerprints your device
LinkedIn's hidden JavaScript routine collects extensive user data without disclosure, raising concerns about covert surveillance practices.