#logging-error
#logging-error
[ follow ]
fromDevOps.com
1 day agoIs Your AI Agent Secure? The DevOps Case for Adversarial QA Testing - DevOps.com
The most dangerous assumption in quality engineering right now is that you can validate an autonomous testing agent the same way you validated a deterministic application. When your systems can reason, adapt, and make decisions on their own, that linear validation model collapses.
Information security
#opentelemetry
DevOps
fromDevOps.com
3 weeks agoHow eBPF and OpenTelemetry Have Simplified the Observability Function - DevOps.com
OpenTelemetry eBPF Instrumentation enables automatic observability without manual setup, allowing engineering teams to gain rapid visibility into services and infrastructure while avoiding instrumentation challenges.
Web development
fromTheregister
3 weeks agoBrilliant backups landed web developer in big trouble
A website migration oversight caused a two-year disconnect where office staff viewed outdated content due to hardcoded DNS settings, while the client only discovered the issue when accessing the site from the office.
fromTheregister
3 weeks agoSysadmin fixed blustering Blackbeard's PC in seconds
He stormed up to my desk, leaned over my partition, and began his rant before I could so much as say hello. He screamed about the rubbish laptops and IT systems we had, nothing ever worked, all the usual stuff. The user's rant ended with a thundered 'Just FIX IT!'
Digital life
Web frameworks
fromMedium
3 weeks agoWhy Most Spring Boot Apps Fail in Production (7 Critical Mistakes)
Spring Boot production failures stem from seven critical mistakes including improper dependency injection, configuration errors, and resource management issues that developers can systematically avoid.
Java
fromNew Relic
4 weeks agoDemystifying Java Instrumentation: The Engineering Behind the New Relic Java Agent
The JVM loads Java agents early via premain method, registering class transformers to intercept and modify bytecode before class execution, enabling runtime monitoring without source code changes.
Business intelligence
fromDevOps.com
1 month agoWhy OpenTelemetry Is Paving the Way for the Rise of the Observability Warehouse - DevOps.com
OpenTelemetry adoption drives observability architecture toward unified warehouse models that centralize logs, metrics, and traces for scalable, cost-effective real-time operational intelligence.
fromTheregister
1 month agoServer crashes traced to one very literal knee-jerk reaction
It was the time of Novell networks, RG58 cables, and bulky tower PCs. It was also a time before the telemarketer's IT department employed specialists. Carter and his two colleagues - boss Mike and part-time student Stefan - therefore handled tasks ranging from programming to support, and everything in between.
Software development
#log-management
DevOps
fromNew Relic
1 month agoLogs Intelligence Evolution: No Silos. Visibility. Zero Code
New Relic introduces Federated Logs and no-code parsing to enable local log querying while maintaining compliance, reducing troubleshooting time from hours to minutes without data movement or manual regex work.
Node JS
fromThe NodeSource Blog - Node.js Tutorials, Guides, and Updates
5 months agoIntelligent Observability: How AI is Transforming Node.js Telemetry into Actionable Optimization
N|Sentinel uses AI integrated with N|Solid to detect Node.js anomalies, analyze runtime behavior, and provide real-time actionable insights to prevent performance issues.
DevOps
fromNew Relic
3 weeks agoeBPF Network Metrics for Kernel-Level Observability | New Relic
New Relic's eBPF-based agent unifies network performance, APM telemetry, infrastructure metrics, and logging into a single lightweight solution, eliminating network blind spots and reducing mean time to innocence during incidents.
fromTechRepublic
1 month agoMicrosoft Starts Testing Built-In Sysmon Monitoring in Windows 11
Sysmon has long been part of Microsoft's Sysinternals toolkit, widely used by security teams to track detailed system activity and spot suspicious behavior. Until now, it had to be downloaded and installed separately. With this update, Sysmon is becoming a built-in Windows feature. "Windows now brings Sysmon functionality natively to Windows," the company wrote. "Sysmon functionality allows you to capture system events that can help with threat detection, and you can use custom configuration files to filter the events you want to monitor."
Information security
fromNew Relic
2 months agoTraditional Network Monitoring is Failing
For any IT department, these four words are the beginning of a familiar, often frustrating, journey. In our modern world, where business success is built on distributed applications and hybrid cloud architectures, the network is the circulatory system. When it fails, everything grinds to a halt. Yet, despite its critical importance, it often remains a black box-a source of blame that is difficult to prove or disprove.
Information security
fromDevOps.com
1 month agoWhat to do About AI's Forced Rethink of Reliability in Modern DevOps - DevOps.com
For years, reliability discussions have focused on uptime and whether a service met its internal SLO. However, as systems become more distributed, reliant on complex internet stacks, and integrated with AI, this binary perspective is no longer sufficient. Reliability now encompasses digital experience, speed, and business impact. For the second year in a row, The SRE Report highlights this shift.
Software development
fromTheregister
2 months agoMicrosoft does something useful, adds Sysmon to Windows
The functionality arrived in the Dev and Beta Windows Insider channels this week in builds 26300.7733 and 26220.7752, respectively. It allows administrators to capture system events via custom configuration files, filter for specific events, and write them to the standard Windows event log for pickup by third-party applications, including security tools.
Information security
Software development
fromDbmaestro
4 years agoIf You Don't Have Database Delivery Automation, Brace Yourself for These 10 Problems |
Manual database processes break DevOps pipelines; only 12% deploy database changes daily, causing configuration drift, frequent errors, slower time-to-market, and reduced productivity.
fromDbmaestro
4 years agoWhat is Database Delivery Automation and Why Do You Need It?
Manual database deployment means longer release times. Database specialists have to spend several working days prior to release writing and testing scripts which in itself leads to prolonged deployment cycles and less time for testing. As a result, applications are not released on time and customers are not receiving the latest updates and bug fixes. Manual work inevitably results in errors, which cause problems and bottlenecks.
Software development
DevOps
fromSitePoint Forums | Web Development & Design Community
2 months agoWhat is the best way to differentiate between performance testing and a true reliability test system?
Prioritize fault tolerance before resource optimization; automate long-term reliability tests with staged, parallel, and targeted strategies to preserve CI/CD velocity.
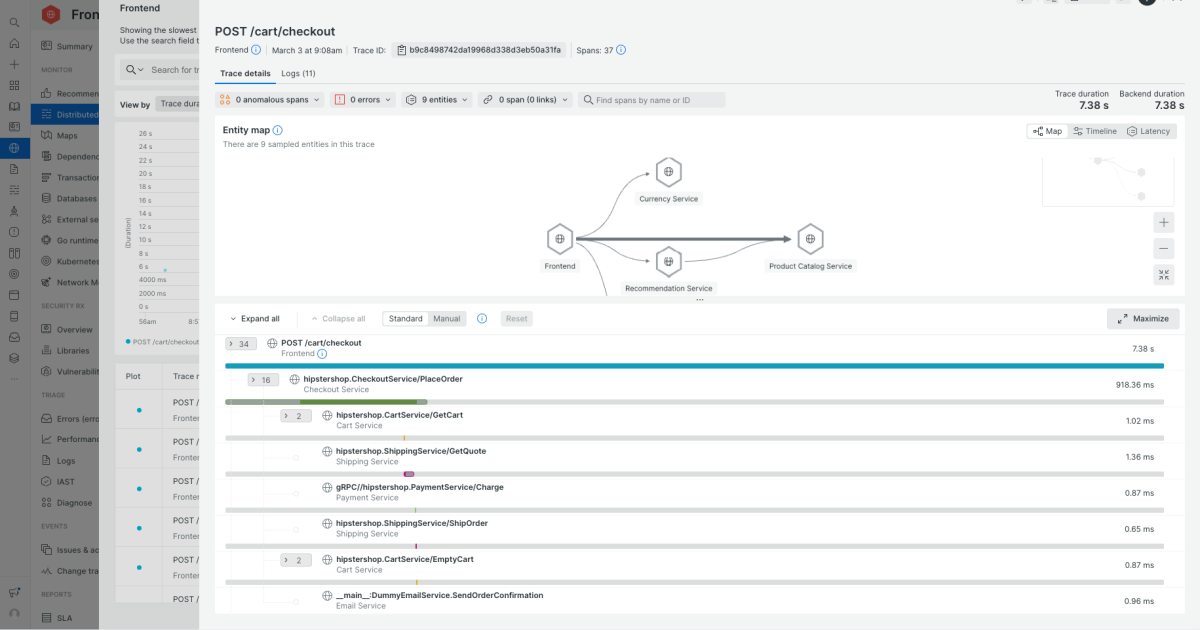
fromNew Relic
1 month ago5 Best Application Performance Monitoring Tools to Consider in 2026
Support for distributed systems. Check how well the tool handles microservices, serverless, and Kubernetes. Can you follow a request across services, queues, and third-party APIs? Does it understand pods, nodes, clusters, and autoscaling events, or does it treat everything like a static host? Correlation across metrics, logs, and traces. In an incident, you shouldn't be copying IDs between tools. Look for the ability to pivot directly from a slow trace to relevant logs,
DevOps
[ Load more ]