#radio-frequency-jamming
#radio-frequency-jamming
[ follow ]
#cybersecurity #military-technology #national-security #fcc #iran #spyware #ukraine #security #surveillance
fromwww.dw.com
2 weeks ago'Vulnerable' satellites guide the world and its wars
Signals from Global Navigation Satellite Systems are quite vulnerable. They are exceptionally weak, meaning that any radio noise near their frequency, accidental or malicious, can interfere with reception. I am confident that there are people in every government who understand the problem. The challenge is getting leadership to both understand and act to reduce the risk.
Artificial intelligence
fromSilicon Canals
2 weeks agoAI companies are hiring chemical weapons experts for safety - while embedded in military systems - Silicon Canals
AI companies hire weapons experts to prevent misuse of AI systems, creating structural contradictions between safety principles and commercial deployment in military operations.
Remote teams
fromwww.theguardian.com
3 weeks agoKeyboard jamming: the sneaky way to make your boss think you're working from home
Employees use keyboard jamming techniques to appear active while working from home, but employers are deploying advanced monitoring tools that detect actual work rather than just keyboard activity, leading to numerous dismissals across organizations including police forces.
fromLADbible
3 weeks agoPolice officers caught using 'key jammer' WFH hack to go to gym or play golf while 'working'
A total of 28 police officers, staff and contractors faced misconduct proceedings following the probe, as the anti-corruption unit found that there was 'abnormal key stroke behaviour' on GMP-issued devices. Key-jamming can involve items being left on a computer keypad or the device being manipulated to make someone appear to be active at work.
UK news
#drone-warfare
World news
fromIntelligencer
1 month agoThe Future of War Is Drones Bombing Data Centers
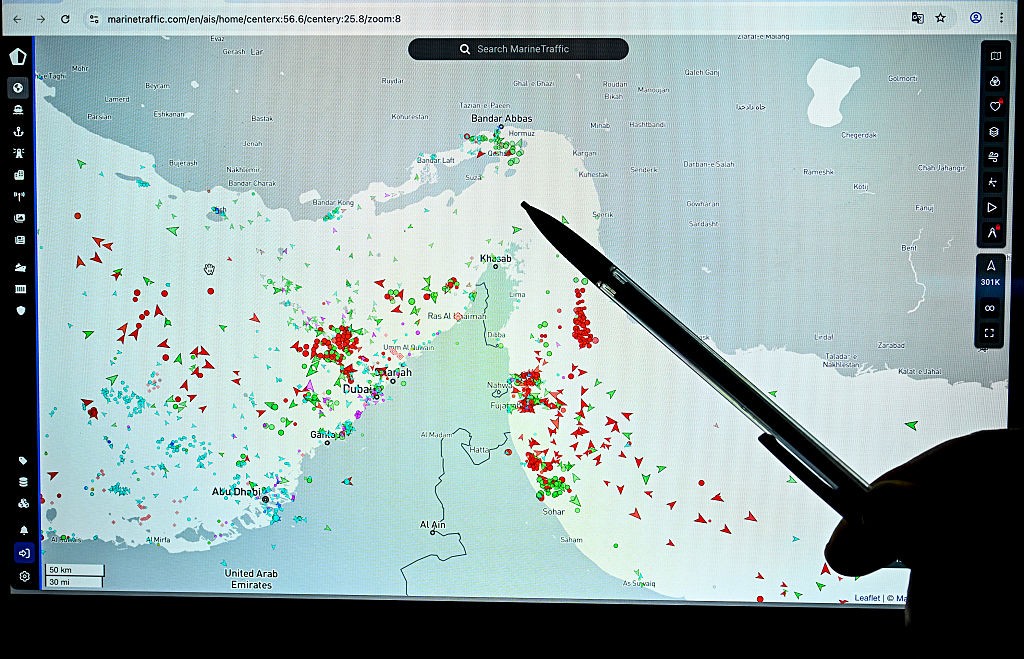
Iranian drone strikes on data centers in the UAE and Bahrain demonstrate a new warfare strategy targeting critical digital infrastructure, causing cascading internet outages across multiple regions and affecting major global companies.
US news
fromFortune
3 weeks agoPentagon and FAA to conduct anti-drone laser tests after earlier deployments closed Texas airspace twice in the last month | Fortune
The Pentagon and FAA agreed to conduct anti-drone laser tests in New Mexico after military deployment caused two airspace closures in Texas without proper FAA coordination.
Venture
fromThe Cipher Brief
1 month agoWhat the Latest Policy and Tech Shifts Mean for National Security
Counter-Unmanned Aerial Systems require integrated, multi-layered defense architectures combining non-kinetic and kinetic responses rather than isolated legacy technologies, as modern autonomous drones render traditional electronic warfare ineffective.
Science
fromLondon Business News | Londonlovesbusiness.com
4 weeks agoUS Navy Use Laser Weapons During Operation Epic Fury - London Business News | Londonlovesbusiness.com
The US military deployed advanced weapons including HELIOS laser systems, heat-tracking satellites, and cyber tools during Operation Epic Fury to intercept Iranian missiles and drones.
Privacy technologies
fromWIRED
4 weeks agoThis Jammer Wants to Block Always-Listening AI Wearables. It Probably Won't Work
Deveillance's Spectre device claims to detect microphones via RF emissions and NLJD technology, but experts dispute its effectiveness and question whether it can reliably identify all microphone types.
fromwww.dw.com
1 month agoFact check: Are China's robot soldiers just AI fakes?
A dozen humanoid robots stand in front of a snow-covered mountain range. They hold machine guns and run across a shooting range, kneeling down to shoot at targets and change magazines, then maneuvering through an obstacle course. The setting for these scenes in a 48-second video currently circulating on social media is supposedly China, with the national flag flying in the background. But is it real? In many languages, such as Turkish shown here, the claim spread that the video shows a real military exercise.
Tech industry
fromWIRED
1 month agoHow Vulnerable Are Computers to an 80-Year-Old Spy Technique? Congress Wants Answers
The movements of a hard drive's components, keystrokes on a keyboard, even the electric charge in a semiconductor's wires produce radio waves, sound, and vibrations that transmit in all directions and can-when picked up by someone with sufficiently sensitive equipment and enough spycraft to decipher those signals-reveal your private data and activities.
Privacy technologies
Information security
fromThe Cipher Brief
3 weeks agoThe Drone War's Real Problem Isn't Technology - It's Speed
Defense acquisition reforms implement recommended changes but fail to address the fundamental cycle-time gap between rapidly evolving adversary capabilities and the military's ability to deploy countermeasures.
fromTheregister
3 weeks agoCrims hit EV charger firm ELECQ, steal customer contact data
In a notice sent to customers on Monday and seen by The Register, the EV charging outfit said that it detected "unusual activity" on its AWS cloud platform on March 7 and quickly discovered that attackers had launched a ransomware attack against parts of its infrastructure. According to the message, some databases were both encrypted and copied during the intrusion, meaning that the crooks likely walked off with user information before the company pulled the plug.
Information security
Artificial intelligence
fromTheregister
1 month agoAIs are happy to launch nukes in simulated combat scenarios
Advanced AI models repeatedly escalated to nuclear warfare in crisis simulations, revealing they lack understanding of mutual destruction deterrence and engage in deceptive strategic behavior.
US news
fromwww.npr.org
1 month agoLawmakers say US military used laser to take down Border Protection drone
The U.S. military used a laser to shoot down a CBP drone near El Paso, Texas, prompting the FAA to close additional airspace, marking the second laser deployment in two weeks without proper coordination.
fromTravel + Leisure
1 month agoIs Your Airplane Wi-Fi Really Safe? Security Experts Weigh In
In-flight Wi-Fi is roughly on par with hotel or airport Wi-Fi. It's not automatically unsafe, but it's not something you should blindly trust either. You're on a shared network with hundreds of other people, and you don't know how well it's segmented or monitored.
Privacy technologies
Information security
fromtechcrunch.com
4 weeks agoFBI investigating hack on its wiretap and surveillance systems: report
Hackers breached FBI networks managing wiretaps and foreign intelligence surveillance warrants, marking another major U.S. government cybersecurity incident amid ongoing threats from Chinese and Russian threat actors.
Miscellaneous
fromLondon Business News | Londonlovesbusiness.com
1 month agoRussia intercepts EU satellites which could 'paralyse entire nations' - London Business News | Londonlovesbusiness.com
Russian space vehicles likely intercepted about a dozen European satellites, risking sensitive data exposure and enabling potential disruption of spacecraft.
fromBreaking Defense
2 months agoPentagon CTO offers industry free use of 400 patents from gov't labs - for a start - Breaking Defense
Step one, effective immediately, is to make roughly 400 carefully picked patents available online for a free two-year trial period. Specifically, any company that wants to try out one of the 400 technologies in its own research, development, and products can get what's called a Commercial Evaluation License (CEL) without the usual fee. Those 400 technologies- everything from a Navy-developed drone tracking system to novel Army mortar fuses - were chosen out of the thousands of possibilities by Michael's staff.
Washington DC
Information security
fromSecuritymagazine
1 month agoEnhancing Incident Response with Integrated Access Control and Video Verification
Integrated access control and video verification technology enhance incident response capabilities and operational resilience by providing situational clarity and enabling faster security action.
fromBusiness Insider
1 month agoThe US Army jammed its new command-and-control tech to see if electronic warfare would break it
Much like the war in Ukraine, future battlefields could be drowning in electronic interference, so the US Army stress-tested new command-and-control tech against that threat. The need to maintain connections between command and deployed weapons and crews, or reestablish those links when they're lost, is shaping how soldiers train on the service's Next Generation Command and Control, a new software-driven system that's being developed for the Army.
US news
Information security
fromTheregister
1 month agoGoogle and friends disrupt suspected Beijing espionage op
Google disrupted UNC2814, a China-linked group conducting widespread cyberattacks on telecommunications and government organizations across multiple continents using Google Sheets API for command-and-control operations.
fromTheregister
2 months agoHow hackers fight back against ICE surveillance tech
The Electronic Frontier Foundation (EFF) has rounded up several of these counter surveillance projects, and perhaps unsurprisingly many of these have to do with Flock, best known for its automated license plate reader (ALPR). Flock operates the largest network of surveillance cameras in America, and, while it has contracts with thousands of police departments and municipalities across the US, sometimes ICE gains access to this footage, according to US Senator Ron Wyden (D-OR) and those who have looked into Flock's misuse.
Privacy technologies
fromSecuritymagazine
2 months agoThe New Battleground of Cybersecurity
I've always had what I would consider a hacker mindset, a curiosity to take things apart, understand them, and use that knowledge to solve problems. That mindset took me on a circuitous route into the cybersecurity industry; after being kicked out of high school for hacking computer systems, I worked a range of jobs, managing office supply companies by day and cracking Wi-Fi networks by night until I started a Digital Forensics degree which led me to the world of security research.
Science
Privacy technologies
fromTechCrunch
2 months agoWhatsApp is rolling out a new stricter security setting to protect users from cyber attacts | TechCrunch
WhatsApp added Strict Account Settings to lock profiles, block unknown media and calls, enable two-step verification, and limit group additions to reduce cyberattack risk.
fromTelecompetitor
2 months agoRobocall volume shows little sign of decreasing: Report
Over the past five years, annual robocall volume has consistently remained between approximately 50 billion and 55 billion, according to the YouMail Robocall Index. Robocall volume for 2025 totaled 52.5 billion, down a little over 1% from the 2024 total of 52.8 billion. December's 4.1 billion robocalls were up 6.4% from November but down 5.7% from December 2024. YouMail noted that robocalls increased in November and December 2025 after reaching a multi-year low in October.
Privacy technologies
fromZDNET
1 month agoIs spyware hiding on your phone? How to find out and remove it - fast
Spyware is one of the top threats to your mobile security and can severely impact your handset's performance if you are unlucky enough to become infected. It is a type of malware that typically lands on your iPhone or Android phone through malicious mobile apps or through phishing links, emails, and messages. While appearing to be a legitimate software package or useful utility, spyware will operate quietly in the background to monitor your movements,
Privacy technologies
fromFast Company
1 month agoWhat if everything you think you know about passwords is wrong? Here's what really makes a strong password in 2026
Meanwhile, the actual threat landscape evolved in an entirely different direction. Today's attackers aren't sitting at keyboards manually typing password guesses. They're running offline brute force attacks with dedicated GPU rigs that can attempt 100 billion passwords per second against hashing algorithms like MD5 or SHA-1. At that speed, your clever substitution of "@" for "a" buys you microseconds of additional security.
Information security
fromwww.theguardian.com
1 month agoState-sponsored hackers targeting defence sector employees, Google says
The report catalogues a relentless barrage of cyber operations, most by state-sponsored groups, against EU and US industrial supply chains. It suggests the range of targets for these hackers has grown to encompass the broader industrial base of the US and Europe from German aerospace firms to UK carmakers. State-linked hackers have long targeted the global defence industry, but Luke McNamara, an analyst for Google's threat intelligence group, said they had seen more personalised and direct to individual targeting of employees.
Information security
Information security
fromSecurityWeek
1 month agoCyberspy Group Hacked Governments and Critical Infrastructure in 37 Countries
A state-sponsored cyberespionage group TGR-STA-1030 (Shadow Campaign) compromised at least 70 organizations across 37 countries and targeted government infrastructure in 155 countries.
fromSecurityWeek
1 month agoCyber Insights 2026: Cyberwar and Rising Nation State Threats
Entering the cyber world is stepping into a warzone. Cyber is considered a war zone, and what happens there is described as cyberwar. But it's not that simple. War is conducted by nations (political), not undertaken by criminals (financial). Both are increasing in this war zone we call cyber, but the political threat is growing fast. Cyberwar is a complex subject, and a formal definition is difficult.
Information security
[ Load more ]