#reset-and-recovery-bug
#reset-and-recovery-bug
[ follow ]
#cybersecurity #microsoft #security #windows-11 #windows-update #ai #data-protection #troubleshooting #observability
fromComputerworld
13 hours agoA core infrastructure engineer pleads guilty to federal charges in insider attack
Rhyne's attack involved unauthorized remote desktop sessions, deletion of network administrator accounts, and changing of passwords, showcasing significant security vulnerabilities.
Information security
#cybersecurity
Information security
fromTechCrunch
2 weeks agoCISA urges companies to secure Microsoft Intune systems after hackers mass-wipe Stryker devices | TechCrunch
Pro-Iran hackers breached Stryker's device management systems and mass-wiped thousands of employee devices, prompting CISA to urge companies to implement multi-administrator approval for sensitive endpoint changes.
Web development
fromTheregister
2 weeks agoBrilliant backups landed web developer in big trouble
A website migration oversight caused a two-year disconnect where office staff viewed outdated content due to hardcoded DNS settings, while the client only discovered the issue when accessing the site from the office.
fromTechzine Global
1 day agoIGEL OS can now run AI models locally on endpoints
AI Armor provides dynamic runtime security and relies on a central policy engine in the Universal Management Suite (UMS) to meet compliance requirements, ensuring that organizations can manage their security effectively.
DevOps
fromTheregister
3 weeks agoSysadmin fixed blustering Blackbeard's PC in seconds
He stormed up to my desk, leaned over my partition, and began his rant before I could so much as say hello. He screamed about the rubbish laptops and IT systems we had, nothing ever worked, all the usual stuff. The user's rant ended with a thundered 'Just FIX IT!'
Digital life
Remote teams
fromNextgov.com
2 weeks agoConsolidation in a complex and aging enterprise IT environment
Federal agencies must pursue strategic IT consolidation to manage aging legacy systems while modernizing, requiring strong leadership, disciplined planning, and change management beyond technological decisions.
fromTheregister
1 week agoJunior disobeyed orders, tried untested feature during demo
Lydia noticed the machine's battery was running low and told two other team members. The more senior went to fetch the backup battery, while the junior team member suggested a quicker method that Lydia firmly rejected.
Gadgets
Business intelligence
fromEntrepreneur
3 weeks agoThe Game-Changing Tech Saving Companies From Data Disasters
Combining Continuous Data Protection with AI capabilities enables businesses to achieve near-zero Recovery Point Objectives and minimal Recovery Time Objectives, preventing data loss and minimizing downtime.
fromZDNET
1 month agoWhy encrypted backups may fail in an AI-driven ransomware era
What if I told you that everything you know and everything you do to ensure quality backups is no longer viable? In fact, what if I told you that in an era of generative AI, when it comes to backups, we're all pretty much screwed?
Miscellaneous
fromTheregister
3 weeks agoDR-DOS rises again - rebuilt from scratch, not open source
The long-dormant DR-DOS.com website is alive again, and DR-DOS 9.0 is in development. There have been six preliminary releases so far this year. The current work-in-progress version is version 9.0.291. This is not the same OS as the DOS-compatible OS that Digital Research developed back in the 1980s, working on the basis of its multitasking multiuser Concurrent DOS OS.
Software development
fromZDNET
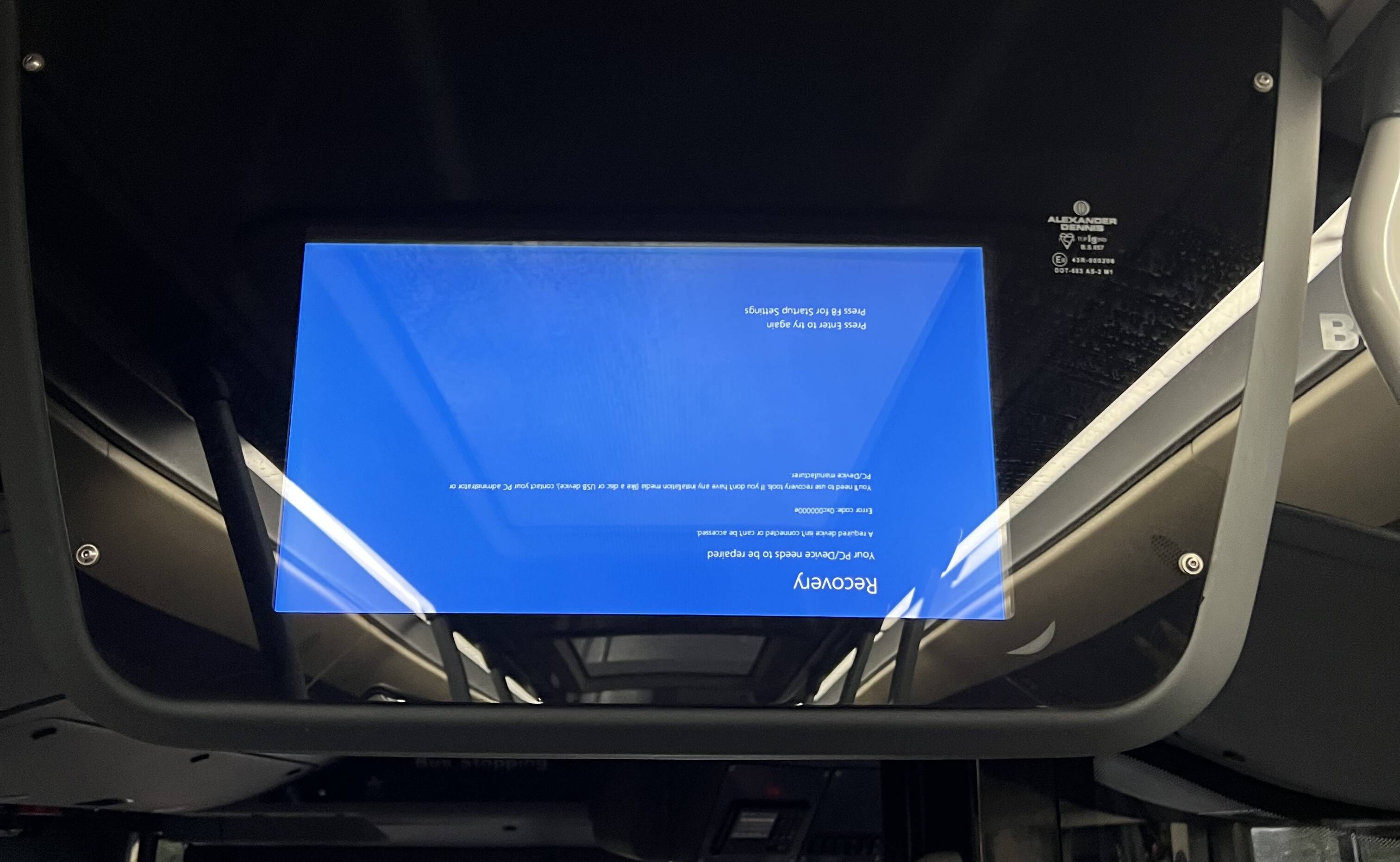
1 month agoYour Windows PC has a secret recovery tool that's seriously useful - here's how to access it
There are a couple of conditions to keep in mind. Using Recovery Drive resets Windows back to its initial factory state. Specifically, the recovery stores all built-in Windows files, any updates installed when you set up the drive, and any customizations from the PC maker. Your customizations, personal files, and any apps you've installed are not included, so you'll want to make sure you have separate backups of those items.
Digital life
fromTheregister
1 month agoServer crashes traced to one very literal knee-jerk reaction
It was the time of Novell networks, RG58 cables, and bulky tower PCs. It was also a time before the telemarketer's IT department employed specialists. Carter and his two colleagues - boss Mike and part-time student Stefan - therefore handled tasks ranging from programming to support, and everything in between.
Software development
fromSecurityWeek
1 month agoHow to Eliminate the Technical Debt of Insecure AI-Assisted Software Development
This extends to the software development community, which is seeing a near-ubiquitous presence of AI-coding assistants as teams face pressures to generate more output in less time. While the huge spike in efficiencies greatly helps them, these teams too often fail to incorporate adequate safety controls and practices into AI deployments. The resulting risks leave their organizations exposed, and developers will struggle to backtrack in tracing and identifying where - and how - a security gap occurred.
Artificial intelligence
Information security
fromTechzine Global
2 weeks agoMicrosoft is blocking automatic Windows installations via WDS
Microsoft is discontinuing automatic Windows network deployments via WDS and Unattend.xml due to security vulnerability CVE-2026-0386 that allows attackers to execute unauthorized code and steal credentials.
Information security
fromThe Hacker News
3 weeks agoDozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices
SAP released security updates for two critical vulnerabilities enabling arbitrary code execution: CVE-2019-17571 in Quotation Management Insurance and CVE-2026-27685 in NetWeaver Enterprise Portal Administration.
DevOps
fromSitePoint Forums | Web Development & Design Community
2 months agoWhat is the best way to differentiate between performance testing and a true reliability test system?
Prioritize fault tolerance before resource optimization; automate long-term reliability tests with staged, parallel, and targeted strategies to preserve CI/CD velocity.
Information security
fromTechzine Global
1 month agoBeyondTrust Remote Support has a critical vulnerability
Unauthenticated remote-code-execution vulnerability in BeyondTrust Remote Support and Privileged Remote Access enables full system compromise; affected versions require urgent patching or upgrades.
[ Load more ]