#traitor-recruitment
#traitor-recruitment
[ follow ]
#cybersecurity #espionage #malware #iran #cia #spyware #drones #ukraine #national-security #russia #north-korea
#cybersecurity
Privacy professionals
fromTechCrunch
2 weeks agoFBI seizes pro-Iranian hacking group's websites after destructive Stryker hack | TechCrunch
The FBI seized two websites operated by pro-Iranian hacktivist group Handala, which conducted cyberattacks against U.S. companies and published information about individuals linked to Israeli military and defense contractors.
Information security
fromThe Hacker News
3 days ago3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don't See It Coming)
Cyber attackers increasingly exploit legitimate tools within environments, making detection difficult and expanding the attack surface organizations must manage.
Russo-Ukrainian War
fromLondon Business News | Londonlovesbusiness.com
4 days agoInvestigations of Russian spy rings and assassination groups grow from UK to Europe - London Business News | Londonlovesbusiness.com
Ukraine uncovered a Russian intelligence network planning contract killings of military commanders and public figures in Kyiv.
fromComputerworld
1 day agoA core infrastructure engineer pleads guilty to federal charges in insider attack
Rhyne's attack involved unauthorized remote desktop sessions, deletion of network administrator accounts, and changing of passwords, showcasing significant security vulnerabilities.
Information security
#national-security
US politics
fromwww.mediaite.com
3 weeks agoTrump Claims to Know Where Iran's Sleeper Cells Are. Why Isn't He Arresting Them?
President Trump claimed federal authorities have identified and are monitoring Iranian operatives who entered the U.S. during Biden's presidency, but reporters failed to press him on this significant national security assertion.
fromSecuritymagazine
2 weeks agoTrump's Former Counter-Terrorism Official Investigated Over Alleged Leaks
Joe Kent, President Trump's former top counter-terrorism official, is under investigation by the FBI's Criminal Division for allegedly improperly sharing classified information. The investigation began months before Kent's recent resignation, according to four individuals with direct knowledge of the probe who spoke to Semafor.
US politics
fromBusiness Insider
3 weeks agoEx-CIA Chief Officer shares a near-death mission that ended in a rush, followed shortly by his divorce
His first wife wasn't in the CIA, and didn't know he worked for the government agency. He couldn't tell her where he'd actually been that day or why he'd sometimes come home late. Even harmless details he couldn't share with her, he said. He'd come home, and she'd ask how his day was, what he'd done, and who he'd interacted with, and he recalled only giving one-word answers like "great," "nothing," and "nobody."
London politics
US news
fromwww.theguardian.com
1 month agoThe Russian honeytrap: alleged spy for Moscow faces five years in US prison
Nomma Zarubina, an FSB-recruited Russian intelligence operative, pleaded guilty to lying to the FBI about her contacts with Russian intelligence while posing as a legitimate activist to infiltrate American political and academic circles.
fromwww.scientificamerican.com
1 month agoHow to win The Traitors, according to science
We watch people lying, and we know they're lying. And also, you watch people dealing with lying not very well and not enjoying it. The lying, backstabbing and manipulation the game inspires does indeed make for delightful TV viewing.
Television
Privacy professionals
fromenglish.elpais.com
3 weeks agoHow the CIA used a former Spanish soldier to keep tabs on Julian Assange
A Spanish security company owner conducted illegal surveillance of Julian Assange at Ecuador's London embassy on behalf of the CIA, placing hidden microphones and monitoring his communications.
Information security
fromSecuritymagazine
4 days agoThe Rising Tide of Executive Protection: Corporations Ramp Up Security in an Era of Heightened Threats
Companies are increasingly investing in executive protection due to rising threats, making it a strategic necessity for business continuity and resilience.
fromThe New Yorker
2 months agoNational Security Begins Behind the Toaster
Dear Secretary Pete Hegseth, I realize that this is a big ask, but would you please invade and take possession of my son and daughter-in-law's apartment? Or maybe you'd like to make them an offer first? Either way, as a concerned mother and patriot who believes that national security begins at home, I feel it's my duty to let you know that Otis and Luna, the co-dictators of Unit 4-C, at 439 Bergen Street, in Park Slope, Brooklyn, must be overthrown.
Humor
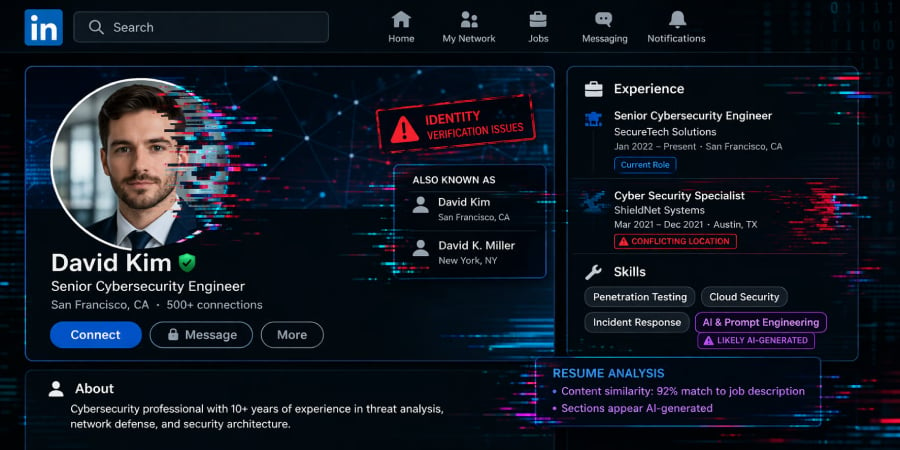
fromNextgov.com
1 month agoNow accepting applications - for classified intel
Over the past year, waves of federal layoffs have left thousands of government employees and contractor clients suddenly out of work. For foreign intelligence services, that disruption has opened new opportunities. With more former U.S. officials seeking employment or freelance work - often in specialized national security fields - adversaries, namely China, have stepped in, posing as consulting firms, research groups and recruiters.
US news
fromThe Cipher Brief
1 month agoThe Kremlin Files: Russian Double Agents and Operational Games
A double agent, by contrast, is an intelligence asset who is knowingly and deliberately directed by one service to engage another in espionage. The controlling service uses that agent to feed information (called feed material) -true, false, or mixed-to the adversary. They do so to simultaneously study the adversary's tradecraft, collection priorities, and decision-making. In the Russian system, double agents also serve a bureaucratic function: they generate statistics, "success stories," and operational narratives that demonstrate effectiveness to political overseers and ultimately to Putin himself.
World news
Information security
fromSecurityWeek
3 weeks agoIran-Linked Hackers Take Aim at US and Other Targets, Raising Risk of Cyberattacks During War
Pro-Iranian hackers are expanding cyberattacks from the Middle East into the United States, targeting defense contractors, medical device companies, and critical infrastructure like power stations and water plants.
fromwww.theguardian.com
4 weeks agoNorth Korean agents using AI to trick western firms into hiring them, Microsoft says
The scam typically involves state-backed fraudsters applying for remote IT work in the west, using fake identities and the help of facilitators in the country where the company targeted is based. Once hired, they send their wages back to Kim Jong-un's state and have even been known to threaten to release sensitive company data after being fired.
Information security
Information security
fromtechcrunch.com
1 month agoFBI investigating hack on its wiretap and surveillance systems: report
Hackers breached FBI networks managing wiretaps and foreign intelligence surveillance warrants, marking another major U.S. government cybersecurity incident amid ongoing threats from Chinese and Russian threat actors.
Information security
fromNextgov.com
1 month agoPotential US-built hacking tools obtained by foreign spies and cybercriminals, research says
A sophisticated iPhone hacking toolkit called Coruna, likely originating from U.S. government development, has proliferated to foreign intelligence agencies and criminal groups, compromising iOS devices through multiple exploit chains.
Information security
fromFortune
1 month agoCyber retaliation from Iran is a problem for U.S. companies - 'It's in the hands of a 19-year-old hacker in a Telegram room,' ex-NSA operative says | Fortune
Iranian cyber operatives compromised a popular prayer app to coordinate civil resistance during strikes, prompting regime loyalists to launch aggressive counter-attacks through decentralized hacker networks.
Information security
fromSecurityWeek
1 month agoIn Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
Predator spyware suppresses iOS indicators through kernel-level access, Russian cyberattacks on Ukraine's energy grid gather intelligence for missile targeting, and Treasury launches AI cybersecurity initiative for financial services.
[ Load more ]