#surveillance-via-apps
#surveillance-via-apps
[ follow ]
#privacy #cybersecurity #surveillance #data-breach #data-privacy #ai #data-collection #advertising #malware
Mobile UX
fromYanko Design - Modern Industrial Design News
1 day agoThis Finnish Privacy-focused Linux Phone Wants You to Forget Google Exists - Yanko Design
Jolla reintroduces a European smartphone ecosystem with its new phone running Sailfish OS, emphasizing privacy and independence from American tech giants.
fromTheregister
22 hours agoNHS staff resist using Palantir software
One official reportedly described Palantir as 'ethically bankrupt' in justifying his refusal to use the software, and noted that he knows of coworkers who deliberately slow their work pace when forced to use the system.
EU data protection
#data-breach
Privacy professionals
fromSilicon Canals
1 day agoA fintech app asked users for their passports - then left 360,000 files unprotected for five years - Silicon Canals
A money transfer app exposed over 360,000 sensitive files on a public server for nearly five years, including unencrypted personal documents.
fromnews.bitcoin.com
7 hours agoThe Retroactive Decryption Trap: Why Post-Quantum Upgrades Can't Save Your Past Privacy
Guy Zyskind emphasized that the whitepaper reframes the conversation around quantum threats, stating that the traditional 10-year migration window now seems dangerously optimistic given Google's findings.
Information security
fromWIRED
1 day agoCBP Facility Codes Sure Seem to Have Leaked Via Online Flashcards
The public Quizlet set contained information about alleged codes for specific facility entrances. 'Checkpoint doors code?' asked one card, with a specific four-digit combination listed in response.
Privacy professionals
fromComputerworld
19 hours agoA core infrastructure engineer pleads guilty to federal charges in insider attack
Rhyne's attack involved unauthorized remote desktop sessions, deletion of network administrator accounts, and changing of passwords, showcasing significant security vulnerabilities.
Information security
Privacy professionals
fromSilicon Canals
1 day agoA money-transfer app stored customer passports on an unencrypted, publicly accessible server for nearly five years - Silicon Canals
Fintech companies face regulatory pressure to collect identity documents but lack enforceable obligations to protect them, leading to data breaches.
Information security
fromSecuritymagazine
3 days agoThe Rising Tide of Executive Protection: Corporations Ramp Up Security in an Era of Heightened Threats
Companies are increasingly investing in executive protection due to rising threats, making it a strategic necessity for business continuity and resilience.
fromMedium
1 month agoSurveillance by default, consent by assumption
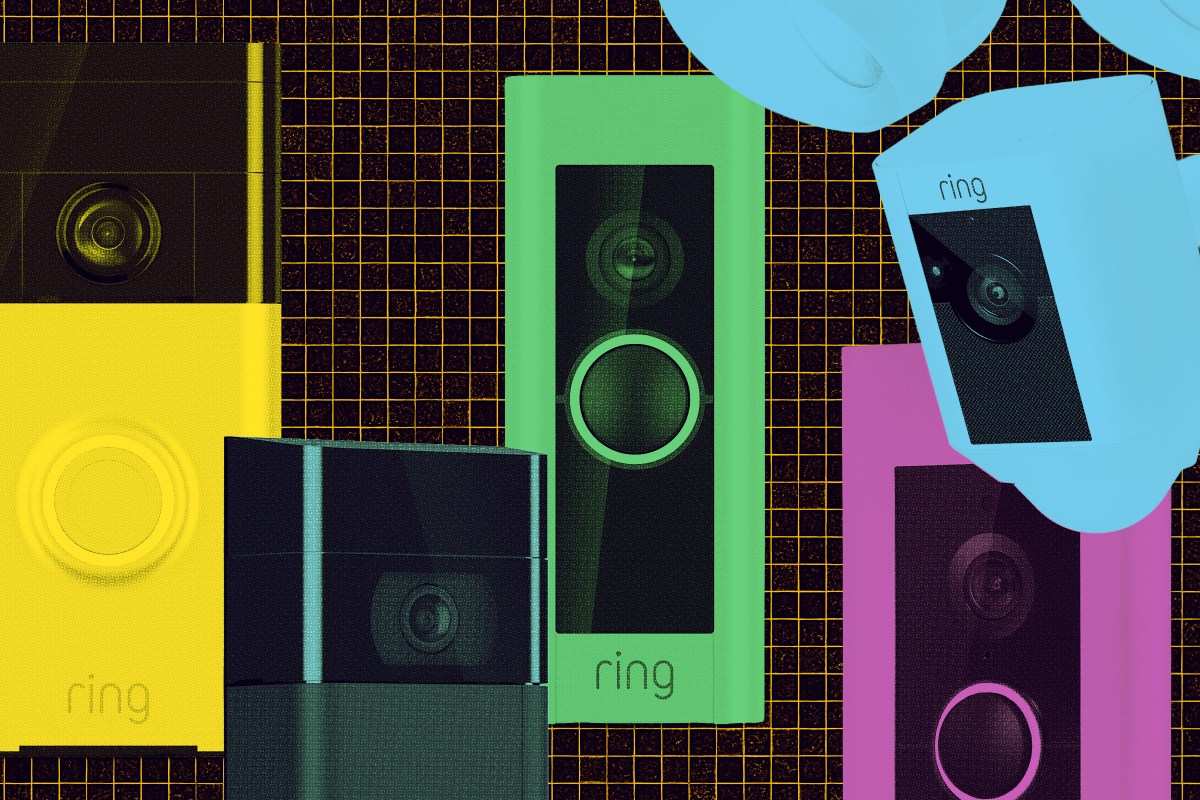
When presence becomes participation Ring's Search Party feature queries nearby cameras when a missing pet is reported. As Senator Ed Markey observed, this closely resembles neighbourhood-scale surveillance infrastructure. Crucially, Search Party does not operate in isolation. Ring's Familiar Faces feature applies facial recognition to anyone passing within camera range, continuously scanning and categorising faces without their explicit knowledge or agreement.
Privacy technologies
Privacy professionals
fromwww.theguardian.com
4 weeks agoWho is responsible for our creeping surveillance age? Chances are, it's you | Tatum Hunter
Surveillance culture, once driven by governments and corporations, now involves civilians monitoring friends, family, and strangers, reflecting widespread desensitization to invasive data collection practices.
fromSlashGear
1 month agoChanging 5 Phone Settings Can Limit The Amount Of Data Apps Collect About You - SlashGear
Only about a year old at that point, the App Store was changing people's relationship with software. Users were growing accustomed to the idea that the smartphone was a digital Swiss Army Knife, its glossy touchscreen waiting to be fitted with the right tool for any job. But what the public had not anticipated as we swiped and scrolled was that our phones might begin to watch us back.
Privacy technologies
Privacy technologies
fromZDNET
2 months agoHeading out to protest? Disable your phone's biometrics, and 6 more ways to protect your privacy
Smartphones empower protesters to communicate and document events but can also threaten privacy; passcodes can offer more protection than biometrics against unauthorized access.
[ Load more ]