#digital-certificates
#digital-certificates
[ follow ]
#data-breach
Privacy professionals
fromSilicon Canals
22 hours agoA fintech app asked users for their passports - then left 360,000 files unprotected for five years - Silicon Canals
A money transfer app exposed over 360,000 sensitive files on a public server for nearly five years, including unencrypted personal documents.
Privacy professionals
fromSilicon Canals
1 day agoA money-transfer app stored customer passports on an unencrypted, publicly accessible server for nearly five years - Silicon Canals
Fintech companies face regulatory pressure to collect identity documents but lack enforceable obligations to protect them, leading to data breaches.
#privacy
Privacy technologies
fromBitcoin Magazine
1 day agoWhat If Your VPN, Phone Number, And AI Chat Left Zero Trace? Meet Nadanada.me - The "Nothing At All" Privacy Revolution
LNVPN has evolved into a comprehensive privacy infrastructure service offering anonymous eSIM data plans, disposable phone numbers, and AI chat tools.
fromTearsheet
2 days agoHow Paze is betting bank trust can crack the digital wallet market - Tearsheet
I'm the general manager of Paze, one of the business units of Early Warning Services. The mandate is really to take Paze and bring this new payment checkout system to the masses - both on the consumer side and on the merchant side - really making sure that our goal of becoming one of the top three wallets for checkout in the next five years becomes reality.
Cryptocurrency
#digital-identity
London startup
fromComputerWeekly.com
2 weeks agoDigital IDs edge closer to practical reality for UK businesses | Computer Weekly
The CFIT's Digital Company ID Coalition has delivered priority use cases, governance frameworks, commercial models, and a working prototype, advancing digital identity infrastructure for UK businesses from concept to practical implementation.
EU data protection
fromwww.thelocal.se
3 weeks agoSweden developing state-issued alternative to BankID
Sweden is launching Sverige-id, a government digital identification service available to citizens and registered foreign residents, addressing barriers foreigners face accessing BankID and essential services.
fromwww.bbc.com
2 weeks agoRace on to establish globally recognised 'AI-free' logo
AI is creating significant disruption and competing definitions of what is 'human made' are confusing consumers. A universal definition is essential to build trust, clarification and confidence. Without standardization, consumers face confusion distinguishing between genuinely human-made products and those using AI, undermining the credibility of the entire certification movement.
Graphic design
Information security
fromnews.bitcoin.com
3 days agoChainalysis Deploys AI Agents to Counter Criminal Use of Artificial Intelligence in Crypto
Chainalysis introduces AI agents to enhance fraud detection and compliance without requiring deep technical expertise, ensuring data quality and human oversight.
Healthcare
fromNextgov.com
3 weeks agoCMS touts early uses of new biometric verification tools for Medicare.gov
CMS launched modern identity verification options (Login.gov, ID.me, CLEAR) on Medicare.gov, with 25% of users adopting them within five to six days and 60% of new accounts using these credentials.
#digital-id
UK politics
fromPinkNews | Latest lesbian, gay, bi and trans news | LGBTQ+ news
3 weeks agoDigital IDs won't require sex and gender data, government confirms
The UK government's relaunched voluntary digital ID scheme will not collect sex or gender information, addressing concerns that it could out trans people.
UK politics
fromwww.theguardian.com
3 weeks agoUK digital ID scheme to have limited use before next general election, minister says
Britain's £1.8bn digital ID scheme will initially offer limited functionality including vehicle tax payments and right-to-work checks by the next election, with broader services like benefits and pensions planned for the following parliament.
Privacy technologies
fromArs Technica
2 weeks agoWorld ID wants you to put a cryptographically unique human identity behind your AI agents
World ID's Agent Kit enables AI agents to prove human authorization through iris-verified identity tokens, allowing websites to distinguish legitimate automated requests from malicious Sybil attacks.
fromEntrepreneur
1 month agoWhy Nations Are Now Battling Over Your Digital DNA
Across the world, governments are redefining data. It is no longer a commercial byproduct, but a strategic resource. One that carries economic weight, political influence, and long-term national consequences. At the center of this shift is what most people never consciously see but continuously produce: their digital DNA.
World politics
Privacy technologies
fromArs Technica
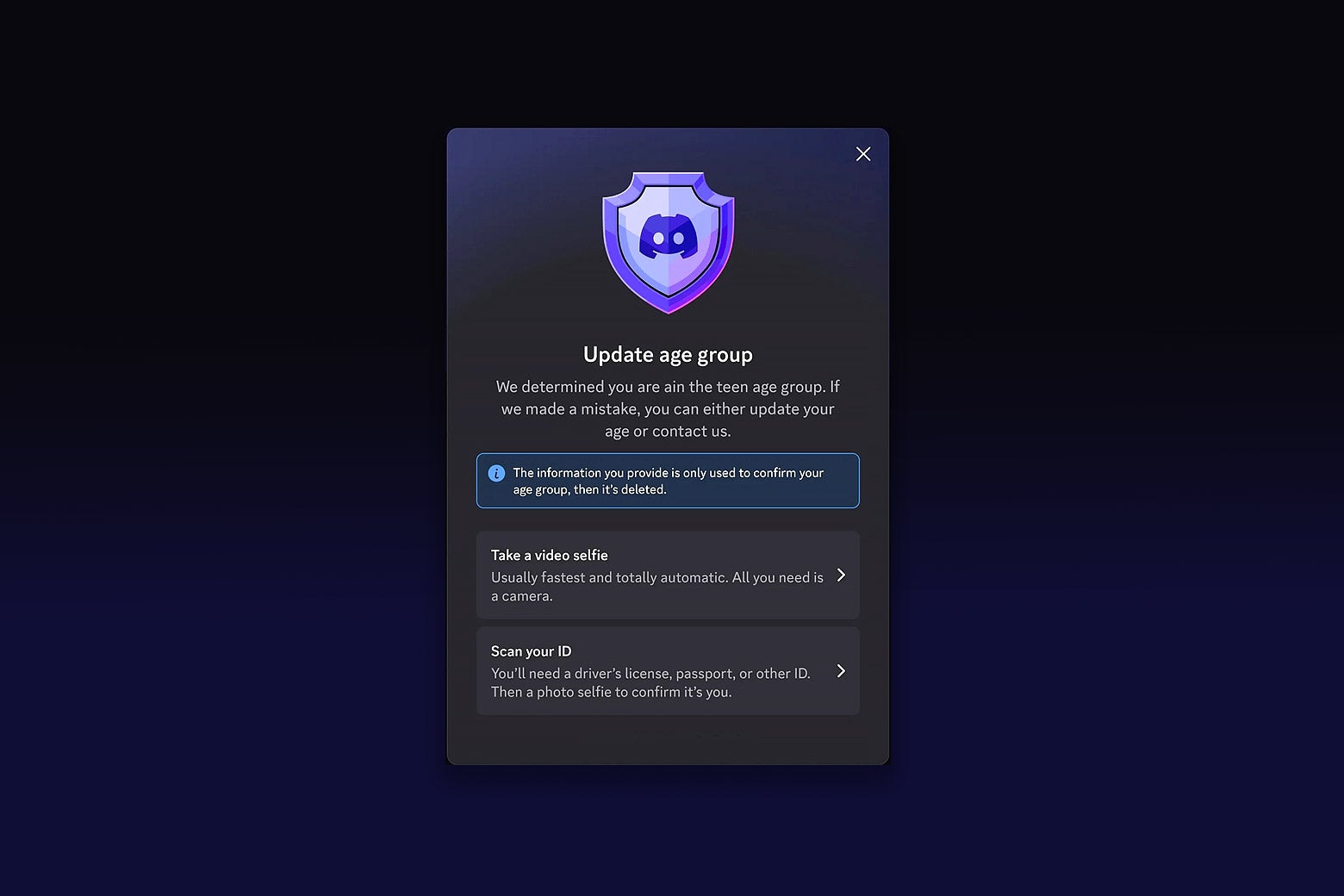
2 weeks agoAfter Discord fiasco, age-check tech promises privacy by running locally. Does it work?
Age-verification systems using on-device face scans and cross-platform age keys reduce privacy risks, but widespread distrust of vendors and past data breaches undermine user confidence in these technologies.
Privacy professionals
fromMedCity News
2 weeks agoThe Evolving Landscape of Privacy and Cybersecurity: Essential Strategies for Legal and Compliance Professionals - MedCity News
Organizations must combine strong controls with comprehensive employee training and accountability culture to effectively protect sensitive data and comply with evolving privacy laws.
Privacy professionals
fromTheregister
2 weeks agoAge verification isn't sage verification inside OSes
California's Digital Age Assurance Act attempts age verification for minors but is vague, incoherent, and creates liability risks without clearly defining compliance requirements or addressing practical implementation across diverse computing devices.
Privacy professionals
fromWIRED
2 weeks agoDo You Need an Identity Protection Service for Safe Browsing?
Identity theft protection services function as insurance products offering reactive compensation for damages rather than active prevention, with coverage details and sub-benefit caps critically affecting actual protection value.
fromFast Company
1 month agoThis crypto ring certifies your digital self with real-life handshakes
Identity spoofing against older adults alone grew by 8x between 2020 and 2024, driven in part by convincing AI impersonations of friends and loved ones. It's a problem costing people in the U.S. nearly half a billion dollars a year with no end in sight.
Privacy technologies
fromSilicon Canals
1 month agoThe global infrastructure of digital ID is being built right now - and nobody voted for it - Silicon Canals
What I walked through wasn't just an immigration gate. It was a node in a rapidly expanding global infrastructure of digital identity, one being constructed at extraordinary speed, across dozens of countries, by a mix of governments, multilateral organizations, and private technology vendors. The people building it believe they are solving real problems: fraud, statelessness, inefficient public services, financial exclusion.
Privacy technologies
Cryptocurrency
fromLondon Business News | Londonlovesbusiness.com
1 month agoCrypto Wallet Development 2026: Modern Guide to Smart Security & UX - London Business News | Londonlovesbusiness.com
Modern crypto wallets must prioritize user-friendly, human-proof security, fast Layer-2 transactions, and institutional-grade features to serve billions of users by 2026.
fromWIRED
1 month agoPassword Managers Share a Hidden Weakness
An FBI informant helped run the Incognito dark web market and allegedly approved the sale of fentanyl-laced pills, including those from a dealer linked to a confirmed death, WIRED reported this week. Meanwhile, Jeffrey Epstein's ties to Customs and Border Protection officers sparked a Department of Justice probe. Documents say that CBP officers in the US Virgin Islands were still friendly with Epstein years after his 2008 conviction, illustrating the infamous sex offender's tactics for cultivating allies.
Information security
fromEntrepreneur
1 month agoAI Can Delete Your Data. Here's Your Prevention Plan.
Never feel that you are totally safe. In July 2025, one company learned the hard way after an AI coding assistant it dearly trusted from Replit ended up breaching a "code freeze" and implemented a command that ended up deleting its entire product database. This was a huge blow to the staff. It effectively meant that months of extremely hard work, comprising 1,200 executive records and 1,196 company records, ended up going away.
Artificial intelligence
Information security
fromSecurityWeek
1 month agoWebinar Today: Identity Under Attack - Strengthen Your Identity Defenses
Adopt an identity-first security strategy to protect sensitive data, meet compliance requirements, and balance security, user experience, and operational efficiency against identity threats.
Information security
fromFortune
2 months agoYou probably use the same password for 30 different websites. It's time for a passkey. | Fortune
Passkeys offer secure, user-friendly authentication but adoption lags due to low awareness, misconceptions, AI concerns, and implementation challenges; treat passkeys as UX initiatives.
fromInfoWorld
2 months agoDescope introduces Agentic Identity Hub 2.0 for managing AI agents
Descope has announced Agentic Identity Hub 2.0, an update to its no-code identity platform for AI agents and Model Context Protocol (MCP) servers. The new release gives developers and security teams a dedicated UI and control plane to manage authorization, access control, credentials, and policies for AI agents and MCP servers, Descope said. Unveiled January 26, Agentic Identity Hub 2.0 lets MCP developers and AI agent builders use the platform to manage AI agents as first-class identities alongside human users,
Information security
[ Load more ]